Nothing Found
Sorry, no posts matched your criteria
Sorry, no posts matched your criteria
The so-called Islamic State recently released a new propaganda video featuring iconic images of Melbourne, interspersed with explosions and IS fighters brandishing firearms in urban combat. What to make of such developments? Should Australia be worried?
The first and most important thing to remember with any new video by IS or a similar group is that it’s pure propaganda, and propaganda is the lifeblood of terrorists. So we need to look beyond the propaganda and what IS wants us to see, to understand what they’re trying to do and why.
Naming or showing specific locations isn’t a new entry in the terrorist propaganda playbook. In 2011 Al Qaeda featured the Sydney Opera House on the cover of its Inspire magazine. In the September issue of the English-language version of its latest magazine, Rumiyah, IS featured a rather unusual ‘poem’ including an apparently random list of Australian place names beginning with the letter B, along with some iconic landmarks. The French, German and Bahasa Indonesian versions of the magazine included the same piece, but with local placenames. As all marketing professionals know, adding local culture and relevance is important to engage with your audience. IS hopes that this might inspire local sympathisers to carry out attacks in its name.
Australia has been named as a terrorist target before. Al-Qaeda looked at conducting an attack during the 2000 Sydney Olympics, and plots were uncovered to attack Holsworthy Barracks in Sydney and targets in Melbourne. The 10 Islamist terrorist plots disrupted by authorities in Australia in the past two years—including the 2016 ANZAC plot in Melbourne—show that the intent remains, but that authorities and businesses are alert to the threat and are working to safeguard against attacks.
We’ve experienced four terrorist attacks during this time, but all at a very low level. Authorities will take this latest threat seriously, but they’ll examine it in context, comparing it with other threat indicators and the intent and capability of local actors.
The latest IS video tells us two things. First, the terrorist group’s ability to direct attacks on these targets is limited, so it’s instead looking to ‘inspire’ others to undertake attacks it can claim. Australia has experienced four such attacks in two years, none of which were directed by IS, but all of which it celebrated as its own.
Second, the video demonstrates IS trying to distract both its supporters and the broader public from what’s really happening to its so-called caliphate and self-declared ‘holy war’. The physical caliphate is essentially no more, having been diminished to a series of safe havens and outposts, and IS has lost the conventional military battle seen since 2014. IS has lost most of its territory and is in retreat, with military defeat likely in the coming year.
The demise of IS as an ostensible ‘state’ highlights another important and interesting factor highlighted by the new video: IS is once again attempting to reinvent its image to compensate for its losses.
Two and a half years ago, Baghdadi infamously proclaimed his so-called state from Mosul’s Great Mosque. Then, and through much of 2015, IS propaganda was dominated by images of the promised land of the ‘caliphate’, showing a comfortable lifestyle, complete with luxury homes and professions. IS offered would-be recruits a migration destination, with its territory differentiating it from its competitors in Islamist extremism.
The latest video couldn’t be more different. The environment is dusty and hard, with IS members shown fighting in the desert and villages, and undertaking attacks. That’s IS attempting to change the narrative. It did that before, when the battle started to turn against it, proclaiming the forthcoming ‘end of days’ with a great battle. Now, as its territory disappears along with some of its supporters, the narrative is morphing a second time to show IS as a fairly standard small insurgency group focusing on attacks.
In this video IS is saying that it’s now focused just on doing what it can to mount small attacks, and it calls upon its supporters to do the same, wherever they are.
IS will continue to focus on inciting and, if it can, directing attacks outside the Middle East to shore up its support base. Australia will remain a target. Some attacks will likely succeed. That’s why it’s important to continue to focus our efforts on removing IS’ base in the Middle East and denying the opportunity that provides to build terrorist networks and skills.

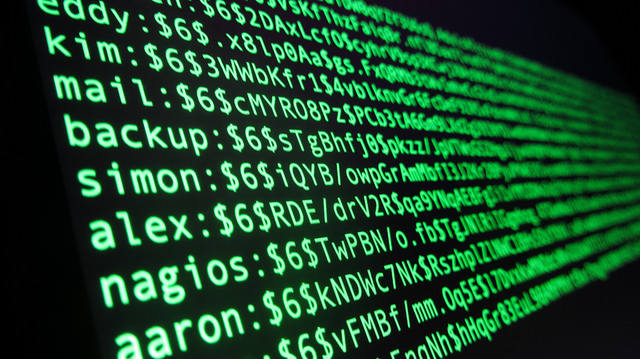
‘Cyber terrorism’ is a catchy term, and appears to have resonated publicly because of the headline appeal and the fear factor. To slap the word ‘terrorism’ on anything ratchets up the hyperbole and disproportionately escalates the sense of threat-related consequences. But is an ‘e-bomb’ really terrorism or is it just hacking?
It’s certainly nothing new. Computer hacking has been happening since the early 1980s—since the widespread advent of computers. A teenager can hack an email account or a database but that doesn’t make them a terrorist.
Terrorists use whatever means available to generate fear. As a largely cyber-dependent society, it’s only natural to assume that cyberspace will be used to achieve that aim in the future.
It’s apposite to explore the potential consequences of a terrorist action initiated within the cyber domain.
At the recent ARPC–OECD Global Terrorism Risk Insurance Conference in Canberra, Lloyds presented a case study, conducted in conjunction with Cambridge University, based on a catastrophic cyber-attack on the US power grid—a highly vulnerable 40 year-old critical infrastructure system. An attack on infrastructure isn’t nearly as visible as a bomb blast and may not result in instant fatalities, but modelling predicts the second- and third-order effects would be devastating. The Lloyds–Cambridge study estimates a cyber-attack targeting the US power grid would result in a bill exceeding $US1 trillion in the most extreme case.
Such an attack is unlikely in the short-term but possible in the future. The 2016 Threat Report (PDF) recently released by the Australian Cyber Security Centre (ACSC) judges that we’re still two or three years away from an attack that could be classed as ‘cyber terrorism’. Although it remains unclear how ACSC arrived at that time-frame, large-scale cyber-attacks against infrastructure are a realistic threat down the line.
The main advantage of a cyber-attack is the absence of international borders. State and non-state actors can operate more covertly in the cyber domain and it can be a more favourable environment for an asymmetric actor. On the other hand, public attention is more important to terrorist organisations than technical complexity. Therefore, terrorists are less likely to expend precious resources on conducting a major attack in the non-physical domain.
IS has proven highly adept at engaging with the cyber domain to inspire individuals, recruit foreign fighters and raise funds, but attacking a digital network is a whole different proposition.
Although it could be assumed that global terrorist organisations have the intent to wage warfare via the cyber domain it seems they don’t currently have the expertise or capability to do so. Hence why the cyber report predicts a two-to-three year timeframe.
Lessons abound for Australian policy makers. When assessing future national security threats, it would be foolish to discount a large-scale cyber-attack with catastrophic consequences. It would be most dangerous if a cyber-attack targeting critical infrastructure or financial systems was conducted in conjunction with a physical attack using other capabilities. This combination of complex attacks would cause the government significant embarrassment, potentially paralyse strategic decision-making and result in a huge propaganda victory for the perpetrators.
State actors are currently more likely to have the necessary intent, expertise and resources to conduct a cyber-attack of the magnitude alluded to in the ACSC report. We’ve seen both China and Russia demonstrate such capability in recent times. But their preference has been for hacking rather than terrorism.
In response to major cyber breaches on the Federal Parliament and Bureau of Meteorology, earlier this year Prime Minister Turnbull pledged $230 million over four years to support the cyber security strategy (PDF). That’s an appropriate and responsible investment for the future but it needs to be just the beginning.
Some of Australia’s critical infrastructure is exposed, to include electricity, water and sewerage, as well as financial systems. We can’t continue to bury our heads in the sand. Thorough risk assessments using a forward looking, systems-thinking approach are needed to secure our nation against future cyber contingencies.
Information infrastructure needs to be further hardened and protected, and closer cyber security collaboration is required between government and the private sector.
On balance, it seems pretty clear that we’re not faced with a brand new threat under the banner of ‘cyber terrorism’. It’s just terrorism executed via the cyber domain, the next phase of an evolving threat. So let’s call it what it is, instead of walking a sensationalist road to nowhere.

Lone wolf attacks are nothing new, but they’ve become more common and increasingly harder to predict over the past 12 months. The threat picture is disparate; some plots show evidence of external direction and coordination, others of collaboration with contacts abroad, while some are one person attacks. For the authorities, a major concern is the low-level of sophistication needed to plan an attack that requires barely any funding, little knowledge of sites and venues, and only rudimentary weapons such as kitchen knives, home-made explosives or motor vehicles. These low barriers to entry have contributed towards copycat attacks.
The profiles of recent attackers and their connection to their purported organisation have called into question our understanding of lone actor terrorist attacks, and how they should be responded to. We need to better understand how these different types of attacks are triggered and how to identify key factors that can prevent similar attacks.
Lone wolf attackers are very different from those participating in organised or directed terrorist cells. Charlie Hebdo, Paris, Brussels, Istanbul and Ankara bombs can all be described as directed attacks. Man Haron Monis (Sydney), Omar Mateen (Florida), Thomas Mair (Yorkshire), Anders Breivik (Oslo), Mohamed Lahouaiej Bouhlel (Nice), Ihsas Khan (Minto)—to name but a few—were all lone actors, and probably not part of a wider cell in their countries.
Directed attacks have been more lethal (PDF). The perpetrators appeared to be working together, demonstrating a strong network of committed radicals across the cities. Unlike lone actors, they possess relevant training, access to materials and in-depth knowledge of how to operate lethal weaponry. In the Paris and Brussels cases, the attackers were previously known to the authorities for various degrees of criminality. The fact that they weren’t considered priority cases raises concern over who the authorities are focused on, and perhaps warrants re-examination.
Clearly there’s no specific profile of a terrorist. Moreover, the degree to which an attacker is politically or ideologically motivated should be reflected in our response to the incident. All the lone actors named above appear to have been motivated by a mixture of political and personal grievances, sometimes combined with possible mental health issues. Some were fascinated with mass murder, some with the myths of jihadi heroism, and some fuelled by anger at Western foreign policies. So it’s difficult to draw a clear line between those using terrorism to air grievances and anger and those who are fully radicalised and committed to a particular ideology or cause. It’s just as important to unpack the motivations behind an attack as it is to respond to it, for this might help identify how to strengthen authorities’ approaches towards preventing future incidents.
For example, the appeal of ‘jihadi cool’ provides an incentive for an individual to morph into the hero figure portrayed in ISIS propaganda. That has enabled lonely, angry and volatile individuals to attach their grievances to a bigger cause, and then to seek retribution whilst attaining grandeur and status. Testimonies from friends, diary entries, internet search histories and galleries of selfies, suggest perpetrators closer to narcissistic adolescents than radical followers of a faith to which they pledge their souls.
Man Haron Monis is a clear example of an individual with a great propensity to showcase himself as being part of something bigger and greater than his reality. His actions prior to December 2014 exposed him as a relentless attention seeker who conflated his personal grievances with his view of the heavenly glow of Islam. The performative nature of his protests unfortunately culminated in the Lindt Café siege. Similarly, Omar Mateen pledged allegiance to Hezbollah during his 911 call, exhibiting not only his confusion about what he was doing, but also demonstrating the incoherent nature of these attacks. Lahouaiej Bouhlel was notoriously promiscuous, irreligious, and only recently interested in radical Islam. Jessica Stern’s research found that often the attacker starts out feeling humiliated and angry that they are viewed as second class. It validates their desire to take on a new identity, often on behalf of a purported spiritual cause; ‘the weak become strong…rage turns into conviction.’
Those individuals exhibit delusions of grandeur and elevated personal grievance, with a willingness to exploit others supported by a sense of entitlement. An ideology such as jihadism is one that lends itself to this narrative and becomes an enabler to justify the narcissist’s actions to the point of violent extremism. Narcissism becomes deadly when destructive impulses are transformed into noble, moral acts.
Rather than being ideologically committed to the cause, the current wave of lone actors is motivated by the ease with which they can attain a symbolic status, justifying an attack by attaching it to a wider cause. It works for both parties; not only does it give the attacker more perceived individual importance, it also adds to the perceived influence of the organisation as more dangerous and more of a threat through racking up numbers of attacks.
Trying to thwart unpredictable attacks is complex and challenging for authorities. Distinguishing between lone attackers who are deeply committed to the ideology of their chosen organisation and those who are franchising the organisation to exorcise personal demons is important, so we don’t contribute to the propaganda being disseminated. Waiting for, and expecting, terrorist organisations to claim an event may unduly—and paradoxically—give a longer lease of life to both the organisation and the perpetrator.

We’ve recently seen the first jihadist terrorist attack in Manhattan since 9/11, after a bomb injured 29 people in Chelsea and several other devices were found in neighbouring blocks and in New Jersey.
But it wasn’t just the crack police work that led to the capture of suspect Ahmad Khan Rahami. Millions were enlisted in the manhunt using digital technology.
Across the city, mobile phones blared with the tone of an emergency alert. The system’s messages, limited to 90 characters and broadcast to all mobile phones using nearby cell towers, had also been used in the city during Hurricane Sandy. But this time the nation’s Wireless Emergency Alerts system was deployed in what’s been called an ‘electronic wanted poster’. It identified a 28-year-old man sought in connection with the bombings in Manhattan and New Jersey. The message was simple: ‘WANTED: Ahmad Khan Rahami, 28-yr-old male. See media for pic. Call 9-1-1 if seen.’
The ‘wanted’ message (and media reports) meant millions of New Yorkers knew his face and could help find the suspect. Rahami was captured several hours after the message went out.
Given Australia’s experience with natural disasters and recent home-grown terrorism, such an emergency alert capability is important. But questions remain as to whether we’re using these services to their full potential.
Location-based emergency alerts, using SMS from all mobile carriers, were first sent to consumers in Victoria in March 2009, after the Black Saturday bushfires ripped through the state a month prior. When catastrophic conditions were expected in early March, the Victorian emergency authorities contacted Telstra and Optus to request an SMS be sent to all mobile services being used in the state. Mobile carriers had only a short time to get the message out. That resulted in some spillage of the message occurring in other states and some Victorian customers not receiving the alert.
In response to the shortcomings highlighted by the Black Saturday bushfires, mobile carriers worked with the federal Attorney-General’s Department to advise on the use of emergency alerts and proposed the development of a standard technical model.
Following this advice, the Council of Australian Governments agreed to the development of a national telephone-based warning system in April 2009.
After a fast-tracked tender process, Telstra was awarded the contract for the system in September 2009.
Unfortunately that approach didn’t provide a solution for all customers at the same time: Telstra only had information on the network-based location of customers on its network and it excluded customers of Optus, Vodafone and the now-defunct 3 network until after the complex contract and technical terms were agreed.
That approach set back by at least two years the delivery of a cost-effective solution available to all customers, regardless of their service provider or their type of service (landline or mobile).
A location-based solution wasn’t available to customers of all mobile networks until October 2013. And it still relies on each mobile carrier being able to detect and locate every mobile phone with a last known location within the warning area set by the emergency services.
There can be practical problems with the service if the message initiator attempts to send messages to a large group, as this can result in queueing and messages arriving late. Those technical limitations can be exacerbated at a time when the community is using the same network resources to communicate with emergency services, family and friends.
If we’re to improve our emergency alert capability to cater for the community’s long-term needs, the Council of Australian Governments needs to engage with mobile carriers and other technology providers through more informal requests for information, to find the most cost-effective way to enable emergency alerts.
Mobile carriers—and other technology innovators—in cooperation with our emergency services and police, are best placed to develop sustainable solutions to emergency alerts. They’ll be most able to leverage changing technologies, such as 5G.
Victoria’s Department of Justice has been given responsibility for tendering and managing a new national contract for emergency alerts. The requirements of the contract will be difficult to meet both from a contractual and technical point of view. The reliance on a single supplier ignores the fact that a number of separate companies will be involved in delivery of the service. Some of the technical requirements may not be feasible, including the obligation to provide radio propagation of the alert area. Nevertheless, the Department hopes to have a provider and a new system confirmed by the June 2018 cutover date. The service will need to be able to reach everyone with access to both local and mobile phone and network coverage anywhere in Australia, regardless of whether they’re at home or travelling, or if they’re an international visitor roaming on Australia’s mobile networks. It’s hoped the contractor will be expected to deliver a ‘technically reliable system’ in extreme catastrophes, and give telephone warning alerts a high level of priority.
Queensland’s already made a move. Following the disappearance and death of schoolgirl Tiahleigh Palmer, the state government has approved new protocols that would allow its electronic notification system, via email or text message, to be used in all state schools when a child has an unexplained absence.
Emergency alerts are designed to make people take notice. They shouldn’t be used for everyday events, and we need to find the right balance to ensure they maintain their impact and keep the community well-informed. To achieve this, there needs to be increased community engagement to determine what situations warrant an emergency alert capability.

There’s a debate going on in the US at the moment that isn’t attracting much commentary here. While it’s a touch arcane, it’s worthy of public discussion. The question is the organisational arrangement for America’s cyber security, cyber offence and signals intelligence capabilities.
The Pentagon and the US intelligence community are in the blue corner, urging President Obama to split military Cyber Command functions away from the intelligence gathering National Security Agency. Senator John McCain, chairman of the Senate Armed Services Committee, is in the red corner, pledging to thwart any attempt to split the two bodies.
Not unusually, Senator McCain has a strong view. His opening statement at a hearing on national security encryption and cyber matters didn’t mince words:
‘Here we go again: another major policy matter has apparently been decided with no consultation whatsoever between the White House or the Department of Defense with this committee. I urge Secretary Carter to provide this committee and the Congress the details of this plan and his reasoning for supporting it. And I hope he will explain what has changed since the last time the administration rejected this idea in 2013…I would remind them that this committee does not take well to being stonewalled while their colleagues in the administration leak information to the press.’
Apart from the Washington beltway shenanigans on public display here, there are some substantive issues underpinning the spat. The organisation split was first discussed in public three years ago, in the wake of the Edward Snowden leaks. The Director of the NSA (DIRNSA) wears two hats; as well as being in charge of the signals intelligence (‘sigint’) gathering function, he has command of the military computer network activities that fall under the Cyber Command.
That command function sits properly under military control because computer network attack can be used to deliver lethal force—in principle, if not to date in practice—through attacks on systems controlling infrastructure where physical harm could result. And, as I’ve argued previously, the military use of cyberattacks is useful as an adjunct to ‘kinetic’ activities in the physical world, by disrupting the ability of adversaries to work out what’s going on and respond in a timely way.
But there’s no requirement for sigint to be under military control. DIRNSA’s counterparts in the ‘five eyes’ intelligence community, including our own Australian Signals Directorate, are all civilians. That doesn’t seem to hinder those agencies from fulfilling their roles, including sigint support to the military. And it’s that military support role that provides an argument for a split. During the 2013 debate, the Director of the Cyber Statecraft Initiative at the Atlantic Council argued that there’s an inherent conflict of interest in having the same person oversee sigint support to the military and command its cyber forces:
‘Imagine if the commander of US Pacific Command were the leading source of information on the Chinese military threat, had the ear of Congress on China policy, ran covert military operations against China, and could decide what information on China was classified. This perverse concentration of power is similar to where the United States has found itself on cyber policy.’
That’d be a strong argument if supporting military cyber operations was all the NSA does. But there’s much more to its role, and I think the rest of its portfolio provides an even better rationale for a civilian Director.
Modern sigint intrudes into civil society through the monitoring of domestic communications, especially in support of counter-terrorism investigations. Those activities came to the fore with the Snowden leaks, which also revealed the (dis)function of the relevant civilian oversight mechanisms. There’s something disquieting about the military presiding over activities that impinge on the civil population and which have civilian oversight.
In 2013 the Obama administration decided against a split, arguing on the grounds of efficiency; ‘without the dual-hat arrangement, elaborate procedures would have to be put in place to ensure that effective coordination continued and avoid creating duplicative capabilities in each organisation’. That argument reflects the historical relationship between sigint and cyber.
The sigint agencies were pulled into cyberspace early on because of the convergence of communication and computer technologies, which saw communications travelling on computer networks as well as ‘traditional’ telecommunication channels. The lure of communications ‘data at rest’ (like emails sitting on computers), which removed the need for real time interception of signals, was too much to resist. The sigint folks started to develop the tools and techniques required to exploit cyberspace.
In that sense there’s a natural synergy between sigint and military cyber operations. Whatever the organisational structure, an exchange of skills and expertise between the two is almost inevitable, and colocation makes sense. But there’s no obvious reason for both functions to be headed by the same person. Making DIRNSA a civilian position would make for better governance, and Cyber Command could properly remain a military position. We’re not privy to why the Obama administration has changed its mind in the past three years, but I think they’ve got it right this time.

In July 2016, Prime Minister Malcolm Turnbull called on his counterterrorism advisers to investigate the mental state of potential ‘lone-wolf’ terrorists. Two months later, Ihsas Khan was charged with a terrorism offence for the allegedly Daesh-inspired knife attack on a grandfather in Minto. Khan had previously been before the courts on larceny and malicious property damage charges, and ordered to undertake a course of psychiatric medication.
At the same time, some political and community leaders, alongside journalists, are showing moral confusion about the correct form of relationship between Australia’s approximately 500,000 Muslim citizens and their fellow Australians. The country’s military forces, including some Muslim personnel, have been at war with Muslim extremists in the Middle East since 2001.
If ever universities had a role to play in studying and explaining violence in the Australian society, now is it. The Vice Chancellor of University of Southern Queensland, Jan Thomas, made an appeal to universities across the Commonwealth to become more directly involved in mentoring students who might be vulnerable to terrorist recruitment during her Chairman’s address to the Association of Commonwealth Universities in July.
The Australian Catholic University is home to two impressive sets of work on the topic, one by Joshua Roose (Political Islam and Masculinity: Muslim Men in Australia 2016) and one by Lazar Stankov on the psychology of extremist mindsets. The latter is exactly what Turnbull seems to be calling for. Jan Ali at the University of Western Sydney has also undertaken valuable community-based surveys.
With support from the federal government, ANU scholar Dr Clarke Jones and Deakin University’s Professor Greg Barton set up the Australian Intervention Support Hub to promote evidence-based research on counter-radicalisation in August 2015.
ANU’s National Security College (NSC), a joint initiative of the university and the federal government, has also stepped up its work in the recent past. In 2014, former government official and law graduate Teneille Elliott started a landmark PhD investigation at the NSC into Australian counterterrorism policy responses. She’s currently studying how we can evaluate the effectiveness and appropriateness of the Australian government’s approach to countering violent extremism and combatting potential terrorism at home. By my estimation, this is the first university-based multi-year evaluation of policy responses in many years.
Yet pockets of excellence such as this don’t address all of the important national research needs as identified by the scholars themselves, or even those specifically identified by the Prime Minister in July. There hasn’t been any sustained surge in related university research on domestic violent extremism since 9/11. Many academics in the field see the amount of funding provided to this research as woefully inadequate and intermittent.
Since 2010, the Australian Research Council (ARC) appears to have funded only one grant focused directly on political science aspects of countering violent extremism, terrorism and radicalisation. As the ARC documentation for a 2016 grant linked to education and radicalisation notes: ‘there is no coherent, evidence-based understanding of young Australians’ perspectives on religions and nonreligious worldviews’ when it comes to terrorism.
The ARC has funded work looking at the citizenship aspects of those issues, for which there’s an urgent need. Ben Saul at Sydney and George Williams at UNSW are leading lights on the defence of ethical approaches to countering terrorism. But Australia doesn’t produce enough research on the causes of terrorism in Australia or the evaluation of political responses to it.
The main explanation of the research deficit in Australia is the way in which we fund social research on interdisciplinary subjects such as countering violent extremism, or other contemporary challenges, such as cyber security and even innovation systems. The ARC isn’t structured to support a knowledge economy in these unconventional fields, a fact acknowledged privately by several government ministers.
A stronger agenda for sustained and consistent research on counterterrorism with impact on the security of Australians should include work in three areas. We need sustained and consistent longitudinal social science and psychological research on perpetrators and possible source groups inside Australia. We desperately need work on the effectiveness of Australia’s law and justice responses, especially at the state and community levels. Importantly, we need research and reflection on ethics: how to find a better balance between protection of human rights (citizenship and freedom of conscience) and promoting a robust counterterrorism strategy.
Our governments, our universities and our communities need to put more faith in the capacity of research to shape a better response to violence in the name of religion.

France’s presidential campaign is heating up, with terrorism constituting one of the key debate topics. In the past 18 months, four terrorist attacks have targeted French territories, from Paris to the small suburban city of Normandy. Fear is tangible amongst the whole population and candidates to the French Presidency must suggest solutions to this critical issue.
However, as the political debates intensify toward the election in April and May 2017, discussions on how to fight terrorism are taking a wrong turn. French public opinion is already exasperated by the strategies taken by politicians; to either scare people about the loss of their national identity or to blindly support the government’s anti-terrorist policies. So far none of the candidates’ declarations have aimed to answer people’s three main questions: how to tackle the roots of radicalisation, how judges should sentence terrorists and how France can efficiently manage the cost of the extended state of emergency.
Politicians have only recently included terrorism in their debates. Questioning France’s response to terrorist attacks was almost taboo before the 14 July Nice attack. In moments of grief, the French population has gathered in solidarity, strongly uniting behind state security policies. Similarly, politicians didn’t challenge the government’s response to the attacks. That consensus no longer stands.
Nicolas Sarkozy, President of the ring-wing party Les Républicains and an official candidate in the presidential election, started the criticism. Sarkozy argues that President François Hollande has underestimated the means required for effective antiterrorist policies. But the Répulicains party is divided between two election strategies regarding terrorism. Sarkozy unveiled his program in his book published on 26 August, Tout pour la France. He demands less immigration and a strict assertion of France’s identity against the minority of Muslims who challenge secularism. Sarkozy’s strategy is to toughen his program to bring back his former electorate, which has partly turned to the far-right. On the other hand, Alain Juppé, Sarkozy’s main opponent in the party, follows a traditional centre-right strategy. He too criticises Hollande’s antiterrorist policies, but argues that Sarkozy plays on people’s fear and threatens France’s impressive solidarity.
On the other hand, Hollande focuses his communication strategy on the improvement of the French economy. Growth has—slowly—returned and unemployment is starting to decrease. Hollande still believes that economic and social issues should be core topics of his presidential campaign, over terrorism. Ministers even assert that challenging current anti-terrorist policies threatens national security.
By refusing to challenge or justify the government’s anti-terrorist policies, socialist candidates, and more broadly all left-wing candidates including the far left and the Greens, risk leaving this critical issue in the hands of right and far-right candidates. Such electoral strategies have been unsuccessful because they don’t address people’s real concerns about terrorism. This is detrimental to France’s democracy.
No candidate has a clear counter-radicalisation strategy, especially for teenagers and prisoners. Last June the General Inspector of French jails published a very critical report on the ability of prisons to reduce the increasing problem of penitentiary radicalisation. Candidates should fully tackle this problem, which deeply concerns the French public. There’s a broader question of how the French judicial system can firmly deal with members of terrorist groups without threatening the rule of law during the state of emergency. In a speech on 8 September, François Hollande tried to explain how his anti-terrorist policies haven’t weakened the French constitution and civil rights, but he was vague and unconvincing.
The candidates’ strategies should also respond to the population’s questions about the economic and human costs of security policies during an extended state of emergency. The first duty of democratic States is to ensure the protection of their population, whatever the cost. However, the state of emergency is increasingly expensive. For instance, the deployment of only military troops in France’s main cities, the Opération Sentinelle, costs €1 million a day. France’s budget has easily managed these costs so far, but future voters need to be reassured about how the budget impact of an extension of the state of emergency until the presidential elections next May.
The human cost of the state of emergency is also worrying, with soldiers and policemen exhausted after months of relentless patrols across French territory. The public expects concrete explanations on how the state of emergency will be extended. Presidential candidates should respond to these concerns in their strategies.
The public also wants to know the financial impact of terrorism on the French economy, which is just starting to improve after years of crisis. Tourism is a crucial activity for the national economy, France being the world’s first tourist destination. The impact of terrorist attacks has been considerable, with 9.9% fewer tourists in Paris so far this year.
Polls repeatedly show that a large majority of the population don’t want Sarkozy or Hollande as candidates, but none of the candidates’ declarations seem to tackle terrorism the way French public opinion expects. Instead, the most vocal candidates are currently playing on people’s fear, for instance with the burkini ban. French communities have remained united so far, but unaddressed political divisions on security policies and national identity are actually playing into the terrorists’ game.

This piece is drawn from Agenda for Change 2016: strategic choices for the next government.
The day-to-day focus of most of a government’s time in office is on matters seemingly unrelated to terrorism and counterterrorism. Social policy, the economy, employment, industry and defence are among the things that will most regularly come to the government’s attention and absorb its time. But when terrorist attacks occur, the government’s attention will be focused on nothing else.
The incoming government’s time in office will witness both terrorist attacks in Australia and attacks overseas affecting Australians and Australia’s interests. Australians will continue to feature among the perpetrators and supporters of terrorism.
Three-quarters of post-9/11 attacks and disrupted plots in Australia have occurred since September 2014, when Australia’s terror alert level was first raised to ‘PROBABLE’ (a terror attack is likely). Australia has experienced three attacks and nine disrupted plots to date. Around 110 Australians are fighting in terrorist groups in Iraq and Syria, 50–59 have been killed and around 40 have returned to Australia. Another 177 have been prevented from leaving Australia through passport cancellation, and 33 have had their passports suspended. Agencies are currently investigating around 400 terrorism cases.
Plenty of government resources have been invested in counterterrorism. The public reasonably expects that the threat of terrorism will be contained, plots will be disrupted and—importantly—a clear and well-exercised response capability will be demonstrated should an incident occur. Work done by law enforcement and security agencies to date to counter terrorism and violent extremism has held Australia in good stead, but this is a dynamic area for policy. Effective counterterrorism requires ongoing attention and incremental improvement.
Many counterterrorism-related programs and initiatives are in place under the Commonwealth, state and territory governments. But there’s no shared strategy, framework and plan linking and directing them towards collective goals. There’s also no common platform of easily accessible information communicating Australia’s counterterrorism efforts to the Australian public and the international community.
A strategic plan for counterterrorism should explain the terrorist threat, what the government’s doing and what it plan to do, and provide a structure to guide future activity. The 2015 Counter-Terrorism Strategy provides a foundation for this work, as it describes a shared vision of the problem and work that’s underway.
The strategic plan for counterterrorism would take that further to direct and frame future shared activity and provide guidance to all stakeholders—the Commonwealth, states and territories, businesses, community—on the full program of activity. The plan could also provide the basis for a public counterterrorism annual report.
Regular counterterrorism training exercises for Australia’s decision-makers would put the government in the best position to respond to a real life attack. Scenarios informed by real assessments across the threat spectrum should be used regularly to familiarise the Prime Minister, the premiers, relevant ministers, statutory office-holders and commanders with what they must do when an incident occurs.
Australia could benefit from formal, ongoing programs and procedures to review the exercise and draw lessons from and for all stakeholders, consisting of:
Sharing information—particularly classified intelligence—with those who need it to perform their counterterrorism roles remains a challenge. The Commonwealth Government is best placed to lead in that domain and should establish a mechanism to optimise the sharing of sensitive information and intelligence between Commonwealth and state government agencies.
Countering violent extremism requires a complex and multifaceted response. The most effective interventions will be at the local level and driven by the community. Government can add the greatest value to this cause by facilitating and supporting such actions and giving stakeholders the opportunity to share their experiences and program knowledge, as well as raising public awareness.
The Commonwealth should sponsor the establishment of research and practitioner networks and a resource database of educational material for stakeholders, including educators, the media, vulnerable communities and youths.
Another powerful role for government is in countering online extremist narratives. The Commonwealth could work with both domestic and international partners to provide a strong and active voice across all forms of media explaining Australia’s counterterrorism methods and countering the claims and narrative of extremists. This could be complemented by community and youth group-led initiatives.
The business sector and the broader community also have the potential to be significant enablers in Australia’s counterterrorism efforts. There should be increased engagement with business, industry, the media and community groups to prevent, respond to and recover from terrorism.
Our near region makes countering extremism and terrorism of integral importance to Australia. The incoming government should consider developing a counterterrorism and CVE initiative in partnership with our neighbours, focused on Southeast Asia and the broader Asia–Pacific. Australia could also help develop regional capability by promoting a regional CVE network and resource database.
Counterterrorism is a complex area of policy. There are few, if any, quick fixes, and most policy, operational and legal actions taken to counter terrorism and extremism have a downside and potential unintended consequences. To be effective, counterterrorism activities and programs must be well considered and put in place for the long term.
The Commonwealth Government can take the lead in bringing the various stakeholders and issues together and providing common strategy, guidelines and resources to counter terrorism and violent extremism. Without a coordinated response, Australia risks being surprised when the next attack occurs and suboptimal in our response to it.
I was thrilled to see that ‘ASPI suggests’ recently made reference to Star Wars—the film series, not the missile defence system—by way of a September 2009 article from The Economist on the lack of counterinsurgency tactics in the original sci-fi blockbusters. The publication explained that the movie-going public ‘hate insurgency and counterinsurgency.’
This might have been true in the era of Star Wars’ cinematic release in the aftermath of the Vietnam War, and nuclear war with the Soviet Union still a prevalent concern. But it couldn’t be further from the truth in 2015. In fact, we’re fascinated by insurgency these days. Conceivably, that’s because we are bombarded with news about rebel groups all over the world every week, be they in Syria, Ukraine, Libya, Thailand, Kurdistan or further afield.
Perhaps unsurprisingly, the popular science fiction of the day says a lot about the society in which it emerged. Without wading into the great depths of literature, I’ll offer a few print examples: HG Wells’ The Time Machine (1895) is a diatribe on industrial relations and socialism, George Orwell’s Nineteen Eighty-Four (1949) emerged just after Europe had been torn apart by totalitarianism, and William Gibson’s Neuromancer (1984) was published just three years after IBM released its first personal computer and the internet was in its infancy. A review of recent popular films reveals the ongoing fascination with insurgency and terrorism.
Interestingly, in recent insurgency-themed science fiction, the protagonists are often the ones waging asymmetric war against the overbearing, centralised power. Recent examples include the Hunger Games, Divergent, Red Dawn (the remake)—even The Matrix. I would argue that insurgency fascinates us because of the morally ambiguous challenge it presents. The modern Middle East–North Africa theatre is a perfect example: the West provided support for insurgencies against Muammar Gaddafi and, in the early stages, against Bashar al-Assad. Nowadays, determining which Syrian rebel groups are ‘freedom fighters’ and which are ‘terrorists’ has worse odds than successfully navigating an asteroid field. We have made political choices between supporting status quo dictatorships or pro-democracy activists—just look at Egypt in 2011–13. During the Cold War, the West supported anti-Communist insurgencies, including the jihadist mujahedeen in the Soviet–Afghan War.
Star Wars is useful for analogies because of its pervasive cultural presence. Recent articles have used Star Wars to comment on cyber security, military strategy, religion and just war. It’s easy to turn it into a terrorism caricature, too: Luke Skywalker was ‘radicalised’ after the murder of his Aunt and Uncle by ‘foreign military’ forces and was subsequently responsible for the deaths of hundreds of thousands of imperials (and probably civilians!) aboard the Death Star.
As an avid Star Wars fan, my immediate response to The Economist article was that insurgency/counterinsurgency discourse is more pervasive in more recent Star Wars-related media. The TV series Star Wars Rebels, and the novel ‘Tarkin’ are examples of texts that engage with insurgency themes. But those are contemporary texts, as well. Even in the same ‘galaxy’ as it were, the themes have changed according to the interests of real-world geopolitics.
But if we’re going to be honest, the original Star Wars movies were about fighting fascist dictatorship and the many uses of laser swords. Painting the Rebels as terrorists is just ironic humour, because part of the premise of the film involves accepting that they were fighting for freedom from tyranny. At their best, the films present a canvas upon which to test our ideals for the real world.
For example, there’s a facetious debate over whether Alderaan was a military or civilian target when the planet was destroyed by the Death Star in the original film. Arguing over the merits of Imperial strategy is really a discussion about how far we might be willing to go to preserve our own global political system and the moral minefield that represents.
So when we analyse Star Wars as a counterterrorism text, we’re actually asking under what circumstances we’d support either the Empire or the Rebels. Under which circumstances is the rebel either a freedom fighter or a terrorist? There are no clear answers. We’re constantly debating the merits of security versus freedom, and contemporary terrorism challenges this anew. That’s what makes it such an interesting topic for film.
In Episode VII: The Force Awakens, more than 30 years will have passed since the death of the Emperor—both in the Star Wars galaxy and in our own. A new generation has emerged to continue the struggle between security and freedom; between tyranny and resistance. Where each side will draw the line will be interesting to see. But one thing we can safely assume is that 2015’s audiences will enjoy every minute of it.
 In the lead up to the Paris tragedy, the Federal Bureau of Investigation warned about the dangers of ‘going dark’: data stored on e-mail, text messages, phone calls, live chat sessions, photos and videos being encrypted by terrorists leading to the loss of a previously exploited intelligence capability.
In the lead up to the Paris tragedy, the Federal Bureau of Investigation warned about the dangers of ‘going dark’: data stored on e-mail, text messages, phone calls, live chat sessions, photos and videos being encrypted by terrorists leading to the loss of a previously exploited intelligence capability.
US and French officials have told The New York Times that the Paris attackers may have used difficult-to-crack encryption technologies to organise the plot. Authorities haven’t yet disclosed whether such encryption technology was used by the perpetrators of the Paris attacks.
Law enforcement and security agencies have claimed that encrypted platforms built for commercial purposes to safeguard privacy—where only the sender and receiver hold the keys and devices to decipher the message—are a gift to terrorists and criminals to help them communicate in a way that puts them beyond the law’s reach.
Indonesian terrorism analyst Sidney Jones recently pointed out that ‘many of the committed ISIS supporters from Indonesia are using encrypted communications over WhatsApp and Telegram, not ordinary mobile phone communications that the Indonesian police can tap’.
The mobile messaging service Telegram has emerged as an important new promotional and recruitment platform for ISIL:
‘The main appeal of Telegram is that it allows users to send strongly encrypted messages, for free, to any number of a user’s phones, tablets or computers, which is useful to people who need to switch devices frequently. It has group messaging features that allow members to share large videos, voice messages or lots of links in one message, without detection by outsiders because this service does not run through the computing cloud’.
In January an ISIL follower provided would-be fighters with a list of what he determined were the safest encrypted communications systems. Soon after the list was published, ISIL started moving official communications from Twitter to Telegram.
Both in the US and in the UK there has been a push for technology companies to either ban encryption on the grounds that we’re paying too high a price in terms of security, or at the very least request that companies like Apple, Google and Facebook build ‘backdoors’ that allow law enforcement access into their encrypted tools.
Tech companies have resisted any push to hand over to law-enforcement the keys to their customers’ encrypted data. Privacy advocates have, post-Snowden, defended the technologies as a protection against government snooping.
But tech companies, many of which have been helpful in combating child pornography, are arguing that there are real risks of going along with government requests to access encrypted messages. Apple CEO Tim Cook, for example, recently warned that ‘any back door is a back door for everyone. Everybody wants to crack down on terrorists. Everybody wants to be secure. The question is how. Opening a back door can have very dire consequences.’
The Obama administration recently announced that it wouldn’t push for a law that would force computer and communications manufacturers to add backdoors to their products for law enforcement. They concluded that criminals, terrorists, hackers and foreign spies would use that backdoor as well.
Meanwhile, the NSW Crime Commission’s latest annual report states that ‘uncrackable’ phones have hindered at least two murder investigations in Sydney. NSW police this year travelled to BlackBerry’s headquarters in Canada in a bid to get advice on how to retrieve information from encrypted devices.
I can’t offer a technical solution to this issue. But as I’ve argued before, when it comes to privacy and security, we need to find the right balance in not allowing new encryption technologies to obstruct our counterterrorism efforts.
We need secure encrypted systems for commerce, government and the protection of personal information (our digital identity). Banks and telcos are using those products to safeguard our data. Deliberately weakening encryption solutions would arguably weaken key infrastructure, with the ultimate beneficiaries being criminals, cyber activists and rival nation states.
A cooperative solution with our police and security agencies working with relevant companies to identify the problems would be better than trying to introduce laws to restrict encryption.
Indeed, there’s no guarantee that by banning the use of encryption solutions, as recently proposed in the UK by David Cameron, can be effective. Users and companies might migrate to other countries, solutions, products or servers.
Intelligence agencies will want to be ‘data-holics’ and be able to read all communications—back to the ‘good ol’ days’—so that they can make a judgement if it’s important, rather than need to go to companies on a case-by-case basis.
Instead of handing over the ‘keys to crypto’ there may, however, need to be more effort by our law enforcement and security agencies to strengthen ‘old school’ human tradecraft.
Just as the blind may be able to compensate for their lack of sight with enhanced hearing or other abilities, our security agencies may also need to hone some of their old fashioned skills. Back to the future.